The practice of influencing people to get some confidential data is social engineering. The kinds of details such criminals are searching for may differ, but when people are approached, criminals typically try to con them.
These criminals look for the credentials and bank information or accessing your computer to download some malicious software remotely. The malicious software gives them access to your bank account information or passwords, as well as access to your device.
Social engineering is hazardous because it based on human errors, not on the operating system or computer bugs. Legitimate client errors are less predictable, making them more challenging to track and circumvent than an attack focused on malware.
How Does Social Engineering Works?
In comparison to a virus that relies on encryption methods and malicious code to execute its payload, social engineering relies on human behavior. If done effectively, access to the networks, information, and structures can be exploited.
For instance, rather than spending so long working on the new type of malware, offenders focus their efforts on tricking workers by acting as an IT service specialist to share their code over the phone. The typical attacker may be searching for a flaw in the software to enter a computer system.
Types of Social Engineering
The company must take steps to train staff on specific kinds of attacks in social engineering, like phishing, baiting, pretexting, spear phishing, quid pro quo, and tailgating. There are technical solutions which can counteract social engineering, providing an employee base that can identify and prevent effective strategies of social engineering is the best protection against such techniques.
Baiting
This tactic uses bait to convince you to do something that makes it possible for the attacker to
Infiltrate your device with malware and thus get your personal information. Most social engineers use USBs as a trap, leaving them with tags such as ‘My personal pcs’ in workplaces or parking lots. Curiosity tempts those people who find it, and they use these USBs into their devices. The unknown virus spreads rapidly to their computer.
Once you have installed the malware, the hacker can move into the victim’s device. For digital bait, you see a download link to your favorite classical music, films, or even universal apps that is simply a hidden malicious link that installs viruses on the victim’s device.
Phishing
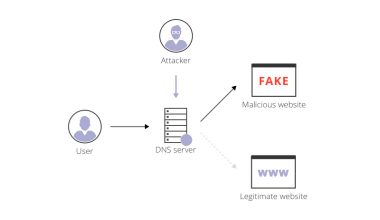
Phishing occurs when emails are used by a cybercriminal to imitate others. They would usually pretend to be your company, bank state, or any other entity which you trust. Their purpose is that you must open the message or download a mysterious file or click the link they give. They want you to be fooled into sharing sensitive data like your social security numbers, login credentials, and bank card numbers.
One of the worst phishing scams make donation appeals after environmental disaster and accidents occur, manipulate the kindness of citizens and encourage them to contribute by inputting private and payment information.
Phishing strategies include a specific target list, with all the entries obtaining the same email so that email services can quickly identify them as spam to protect everyone. But some types of phishing schemes often exist, some of which are quite harmful than the others.
Spear phishing
Unlike the “ordinary” phishing strategies, spear phishing is highly specific at either a particular organization, a particular field within an organization, or even single a worker.
The spear-phishing takes more effort of the hacker because the hacker needs to carry out a complete analysis on the victim, conduct thorough research on everything around the victim, and modify the email that makes it more challenging to differentiate from a genuine email and increases the chances of success for the intruder.
Spear phishing attacks take place in the finance divisions for monetary gain and newer staff as they are more readily fooled into sharing credentials and private information.
Pretexting
Pretexting involves much more analysis than other strategies in social engineering. Pretexting happens when an intruder creates treacherous conditions to force a target to access sensitive information or security systems.
Types of pretext assaults include a fraudster claiming to need confidential data to confirm the recipient’s identification and disguised as a trustworthy person such as an IT department representative to deceive the target into sharing login credentials or allowing access to computers.
Due to the amount of analysis and work they’ve put into building the fake persona, it is difficult to identify such a fraudster. When someone seems too friendly and asks for personal data that you should not share with others, never share these details.
Quid pro quo
Quid pro quo is sometimes considered a baiting subcategory, but what separates it from standard baiting is that the intruder offers something to the victim in return for disclosure of personal data or other direct behavior that will get the intruder what they want.
Such sort of attacks may include any service or activity offered to the victim by the attacker either in return for confidential information or by a valuable prize guarantee.
Vishing
Vishing is a particular kind of phishing. These fraudsters may try to reach you from a responsible entity using an old-fashioned method – the phone. Then, to impersonate you, they must fake their mobile number – it all depends on who you call.
To disguise their identity, these attackers could use pre-recorded text messages, voice messages, or voice-to-text synthesizers. Some even make the assault more persuasive by manipulating people from fraud call centers.
Tips For Defending Against Social Engineering
- Don’t let anyone convince you when it comes to safety that you are too cautious. Scammers also want to target your feelings, sometimes taking advantage of your anxiety and trust, so you need to be vigilant whenever someone tries such an assault.
- If you ever find that someone asks you questions about the things that are typically used to secure your identities, like the name of your first pet, the surname of your wife, your family, etc. Always ensure that you know this guy and confirm that he is a trusted person.
- Training the workers and familiarizing them with these various tactics is essential. You have to grasp the necessary technology techniques in many ways, in addition to your workers. Since social engineering is intended to interact with human behavior, you are a possible target of cybercriminals.
- Many forms of hackers in social engineering may attempt to find some vulnerability in your network and safety backdoors. So it’s essential to keep your software up-to-date.
- Keeping all of your personal and professional accounts secure is very important. The attackers can use your Facebook or LinkedIn accounts to get all the information about you or evaluate your daily life activities.
- You should use a Virtual Private Network Service to protect your personal information and daily life activities. RitaVPN is one of the best VPN services which hide your online activities by changing your IP address. No hackers or data packet sniffers can steal your information.