Pharming is a form of cyber-attack that focuses on harvesting information, which includes login details and passwords to bank accounts, social media networks, credit card details, etc. for the sole purpose of committing financial fraud against you.
In this post, we will be focusing on what pharming is and how you can protect yourself from pharming attacks.
What is Pharming? And how does it work?
Pharming is a combination of two words: ‘Phishing’ and ‘farming’ because it works pretty much like phishing in harvesting your data.
Phishing is a popular form of cyber-attack used by hackers to harvest your information. It involves a hacker sending you malicious emails supposed to be from your financial institution asking you to rectify a fault or problem by clicking on a malicious link to input your information.
The malicious link directs you to a fake website similar to your financial institution’s website. Information you entered on this site is harvested by the hacker and use to gain access to your account to steal your money.
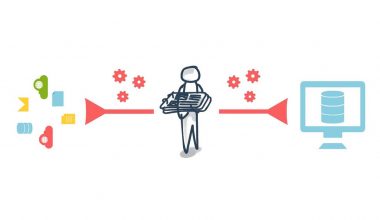
Pharming works pretty much the same way with phishing but does not require or compulsory you click on a link in an email to re-direct you to a fake website.
Instead, hackers using the pharming technique to steal your data find ways of infecting your computer with malware and virus, which changes your host file and automatically re-directs you to a counterfeit website similar to your financial institution’s website.
This happens when you intend accessing your financial institution’s website. What happens here is that the virus, malware, or Trojan horse swaps the original URL for a fake one while you’re trying to type in your financial institution’s URL in the address bar of your browser.
Types of Pharming
Malware-based pharming
The malware-based pharming works by infecting your system with malware like virus and Trojan horses through corrupted DNS cache, infected emails, infected storage devices and downloads, and from infected sites.
The malware corrupts your system host file by replacing the targeted URL (mostly financial institutions and online retail stores) with counterfeit URL.
While trying to access your financial institution or your favorite shopping site, your corrupted host file auto-fills your URL with the counterfeit URL that directs you to a fake website where your data is harvested for financial fraud.
DNS-based pharming
DNS-based pharming works by corrupting the DNS server of targeted institutions, which may include your financial institution. The corrupted DNS server channels data traffic to counterfeit web IP addresses.
Cyber attacks emanating from corrupted DNS servers are always hard to identify and prevent. Hence, there is pretty much nothing you can do against it if not aware of and observant enough about this mode of attack.
How does the DNS-based pharming attack work?
Your data traffic is channeled to The Domain Name System (DNS) server, which are computers that hold the IP addresses of the website you’re visiting. The DNS server re-routes your data traffic to the appropriate website you’re visiting using the website’s IP address, which reflects its location.
For every website you visit, the DNS forms a DNS cache on your system. The DNS cache re-directs your data traffic to the site you’re visiting without having to pass through the DNS server for subsequent visiting.
Pharming-attacks can corrupt both the DNS cache and the DNS server. In the case of a corrupted DNS server, data traffic to an entire network or website is re-routed to a fake website or network, making it possible to harvest information from several individuals, hence the term farming.
How to protect yourself from Pharming attacks?
You should take the following precautions to guide against Pharming attacks
- Watch out for the padlock logo and the ‘s’ in the ‘https’ of the URL of every website you visit. The padlock logo symbolizes that the website you’re visiting has an SSL certificate, and the ‘s’ symbolizes that your data is safe and secure on the network. Therefore, web addresses should look like this: (padlock image) https://www.ritavpn.com/blog/how-to-unblock-websites/
- Avoid clicking on suspicious links from email messages purported to be from a financial institution or other service providers.
- Use a good antivirus software capable of detecting phishing websites and preventing malware infection on your system. Good antivirus software should be able to detect and block suspicious-looking websites.
- Avoid suspicious-looking websites that do not look like your legitimate financial institution’s website.
- Scan removable storage devices with antivirus software before accessing such devices
- Use the two-factor authentication (2FA) feature to verify your login and ensure you’re accessing the right website
- If you have a new router, you should change the default password to protect your network connection
- Use a secure VPN service. The best way of preventing pharming attacks is by using a VPN service with secure DNS servers.
RitaVPN is a recommended VPN service of choice because of its military-grade 256-bit AES encryption protocol, its secure virtual tunnel, and dedicated DNS servers to ensure secure connections with your financial institution, or other websites.
RitaVPN protects your emails, passwords, credit card, and account details, and other sensitive information from hackers on public networks like the Café Wi-Fi hotspot.
Other benefits of using RitaVPN include
- Securely Accessing blocked contents
- Online streaming from geo-restricted streaming services like Netflix US, BBC iPlayer, etc.
- Protection from cybercrime attacks
- Enjoying 100% privacy protection. Hence, with RitaVPN, you can enjoy surfing the net anonymously with no IP leaking, logging of data, online tracking, digital footprinting, etc.
You may also like:
What is Spear Phishing and how to Protect Yourself?
How to protect yourself from phishing attacks
How to Prevent Third-party Apps from Accessing Your Facebook Data?
How to Prevent Common Types of Password-hacking?
How to protect yourself from brute force attacks?
Is an HTTPS Website Safe to Browse?
Visit RitaVPN’s official website to subscribe to any of RitaVPN’s affordable plans and enjoy quality VPN features that keep you protected from cyberattacks.