As most people lack knowledge about the software on the Internet, they subject to Malware attacks. Because of malware software they mostly subject to malware attacks. Cyber attackers reprogram the software that is not for free and allow people to download them for free. When someone downloads and installs that software, the malware that has programmed starts to run in their devices. Unauthorized access to computers, cell phones, laptops, and other devices has been configured by malware. Cybercriminals usually use malware to steal personal and financial information from online users and businesses.
You should know types of malware
Adware
Adware is a relatively innocent type of malware attack that focuses on making money rather than harming your computer. These are aggressive ads displayed on websites and banner ads of application windows. Adware is generally not considered very dangerous. However, most of the ads you have spammed may contain malicious files and links. Usually, Advertisers and Cybercriminals use this, as a way to make quick money.
Spyware
Spyware is made to surprise you. Malicious applications hide in the background and monitor your computer usage and internet browsing activity. It can even change passwords, bank information, and security settings. All the information it collects is sent to a remote user. So you can’t even imagine if spyware is on your device. So your network and traffic can be used as high-level spyware by cybercriminals.
Ransomware
Ransomware is a type of malware that keeps your computer or personal and financial data as a hostage. The malware encrypts all your data on disks or locks you out of your operating system. In both cases, you will receive a message asking you to pay a large ransom to regain access. It is mostly from bitCoins. There is usually a time limit, and all data will be deleted by the message if you don’t follow the payment.
Keylogger
Keylogging is the process by which keys are tracked for a user’s sensitive passwords or for monitoring personal communications.
Trojans
Trojan is a type of malware that masquerades as legitimate software and files. It is reported to be the most common type of malware.
Rootkit
Rootkit is a malware type programmed to provide remote access to your device for third parties.
Worm
Worm seems fairly innocent compared to Virus. The whole purpose of the Worm is to copy it and spread it over the local drive or network. Some worm programs can even be programmed to damage computers.
Virus
Viruses are dangerous malware that can self-replicate and spread to other computers. It is a biological virus. It spreads from host to host and infects as many devices as possible. Therefore, the Virus can be programmed so that the device cannot be restored.
Bots
Although cyber attackers do not use bots widely, they also can cause significant damage. Bot programs are not in the category of malware. But at present, they are using for cybercriminals.
10 signs that can recognize when malware is been installed to your device
Most of the times without knowing that malware has been installed into your device you will neglect it. Therefor your device would destroy without knowingly.
1. Popup Ads
When using the internet if you install apps and software without considering, ads will appear as popup ads on your device whenever you are connected through Wi-Fi networks or data. It can cause your device victimized by malware or adware.
2. Slow computer
The most common symptom of a malware infection is your computer or device to become slower. Want some time to get started on your operating systems and programs? If so, your computer or device may have a virus.
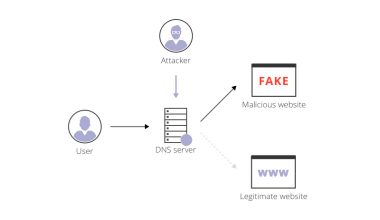
3. Your Browsing Experience
When you are trying to log into any website through your favorite browser, if you are redirected to a website that you do not know, it means your computer or device has been infected by malware. Most of the times your default search engine has been changed. When you try to make a payment or log in to websites about payments, you could victimize by the banking Trojan. In that case, your only clue is the unfamiliar URL in the address bar and find out whether it is real or fake.
4. Changing of Desktop Icons
If you see unusual new icons on your desktop or your icons have been changed you have victimized by an unnecessary program. They are considered as a variant of malware that can collect your personal information and data, spy on your browsing experience and also add toolbars to your browser.
5. Storage becomes full as unusual
If your storage becomes full not in the normal way, it means you have certainly victimized by malware. To take it to the status quo you have to find and permanently remove that malware.
6. Blue screen
This is another way to identify whether your device is victimized or not. If your computer ceaselessly displays a blue screen that tells you that your computer is not healthy and most of the time it happens due to malware. If you do not execute instantly that could damage even to your hard disc.
7. System Tools Are Disabled
If you see that the operating system and the other programs automatically disable regularly, your device is been victimized by malware. Even if the virus guard been victimized, your device has been attacked by malware.
8. If you cannot open any data
If you cannot open any data, you have been attacked by malware like ransomware. So, all the data of yours has encrypted as a black file. If you need to decrypt them back you have to pay to the account given by them in dollars or bitcoins.
9. Mysterious Posts
If massages or posts have been shared through your social media not knowing you, there is a threat in your device which is a malware like BOT.
10. Seems continuous downloads
Due to your carelessness, if you have download and install any software which is not hoped to install and constantly download such software automatically, your device is in a malware attack.
Things that can do to protect from Malware
There are many ways for you to get rid of malware attacks. You can add extra protection by using VPN technology.
Every malware is come from the internet and by using safety measures you can protect from Malware attacks. We recommend you to use a VPN because it helps you to transfer anywhere your data without any obstacle by data encryption. So VPN is the best option to ensure your security and privacy online.
How to Use Computer’s Hosts File to Block Malware and Ads?
How To Scan For Malware With Google Chrome?
WiFi Password Hacker Cause Data Leakage
What is Bloatware? How to Remove it?
How to Recognize and Protect Yourself from Riskware
Shadowsocks vs. VPN: Which One Do You Prefer?
How to detect and remove spyware from your Android & iOS device
How to Protect Yourself from Ransomware?
What is Ad Blocker? How do they Protect your Online Privacy?
Conclusion
Now we think that you have a good understanding of what are Malware types, whether malware has installed to your computer and how to protect from malware. So, as we mentioned above for the protection from that malware you can use a VPN. If you want the best VPN for this, we can recommend RitaVPN as the best VPN.